CMMC Readiness
- Home
- »
- CMMC Readiness
CMMC Compliance Solutions
CMMC Advisory Services
Prepare for CMMC with an Assessor-Aligned Approach
Xylok is a CyberAB-licensed Registered Practitioner Organization (RPO) delivering CMMC readiness services designed around how assessments are performed.
Our CMMC RPO approach focuses on defensible evidence, consistent interpretation of requirements, and eliminating surprises during a formal CMMC assessment.

Simplifying Cybersecurity Compliance
Why Xylok
Unlike traditional consulting firms, Xylok brings the perspective of certified assessors who have successfully supported DoD system authorizations for over a decade.
- Assessor-aligned interpretation of CMMC practices
- Evidence built to withstand real assessment scrutiny
- Fixed-price, structured methodology—not open-ended consulting
- Automation-driven validation using the Xylok Security Suite (XSS)
- Proven success supporting NIST 800-53 and 800-171 assessments
Xylok’s advantage is not just guidance. It’s our execution strategy backed by technical validation and real assessment experience.
A Structured Path to Assessment Readiness
Our CMMC RPO Approach

Phase 1
Boundary & Scoping Foundation
- Establish a defensible CMMC assessment boundary and clearly define what is in scope.
- Identify systems, users, and environments processing CUI
- Validate data flows and trust boundaries
- Define in-scope and out-of-scope assets
- Document assumptions and constraints
Outcome: A clear, defensible scope aligned to assessor expectations
Phase 2
Requirement Interpretation & Standardization
- Ensure consistent and correct interpretation of CMMC Level 2 practices.
- Align practices to NIST 800-171 objectives
- Define expected evidence at the objective level
- Eliminate conflicting interpretations across teams
Outcome: A single, authoritative interpretation of requirements across the organization
Phase 3
Evidence Architecture & Collection
- Build a structured, traceable evidence model that assessors can follow.
- Define evidence requirements per practice
- Establish quality standards
- Build a centralized evidence repository
- Perform initial completeness review
Outcome: Evidence that is organized, traceable, and assessment-ready
Phase 4
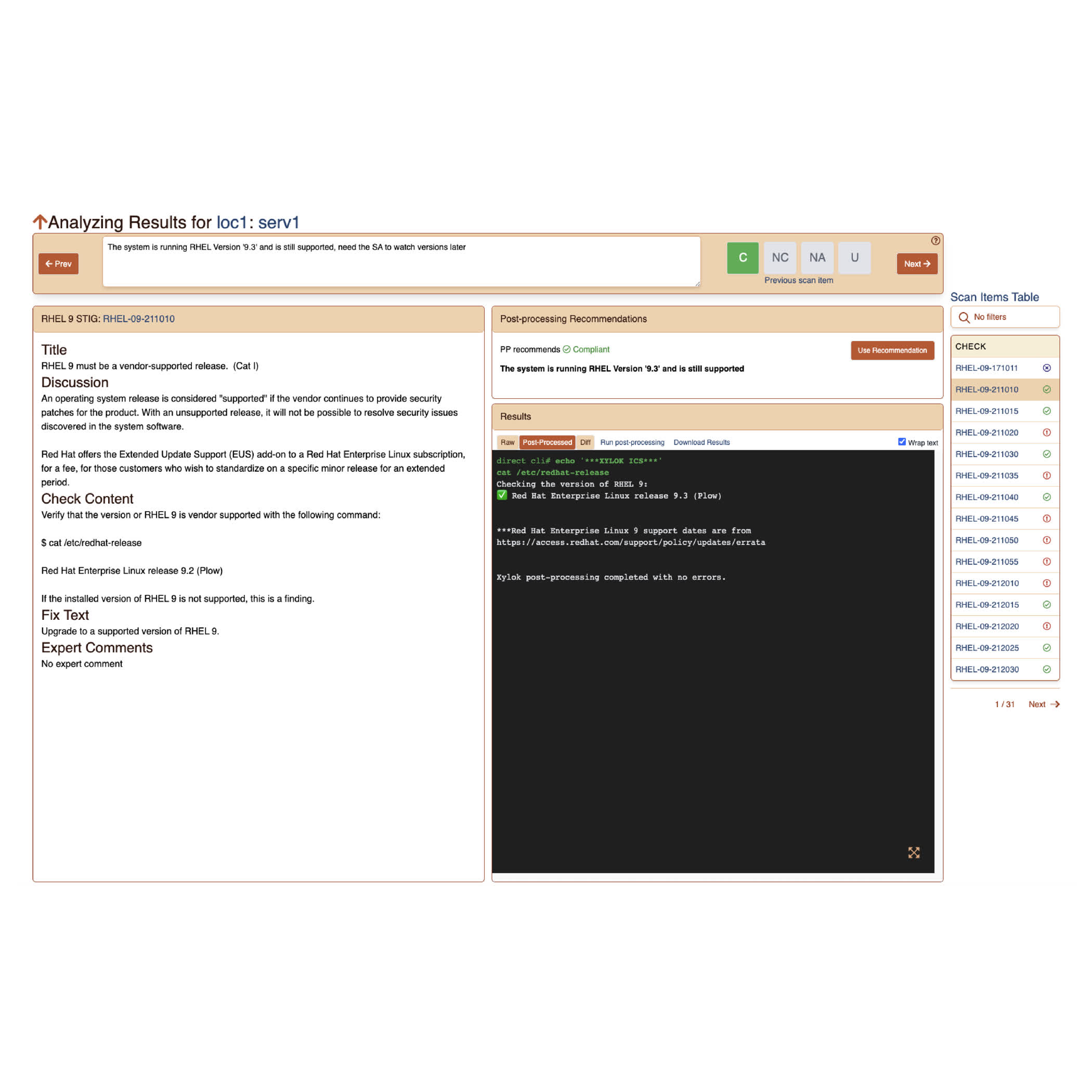
Technical Validation & Gap Analysis
- Validate implementation of technical controls against CMMC intent.
- Automated validation of system configurations
- Analysis of logs and system behavior
- Identification of compliance gaps
- Targeted remediation guidance
Outcome: Verified technical compliance with clearly defined gaps

Phase 5
Documentation & Training Validation
- Ensure all required documentation meets assessor expectations.
- Validate System Security Plan (SSP)
Ensure traceability between practices and evidence - Verify POA&M closure and accuracy
- Confirm training alignment
Outcome: A complete, defensible documentation package

Phase 6
Pre-Assessment Readiness Review
Conduct a final readiness check before formal assessment.
- Mock assessment activities
- Interview preparation for stakeholders
- Final readiness determination
Outcome: Confidence going into the C3PAO assessment—with no surprises
NIST Compliance Solutions
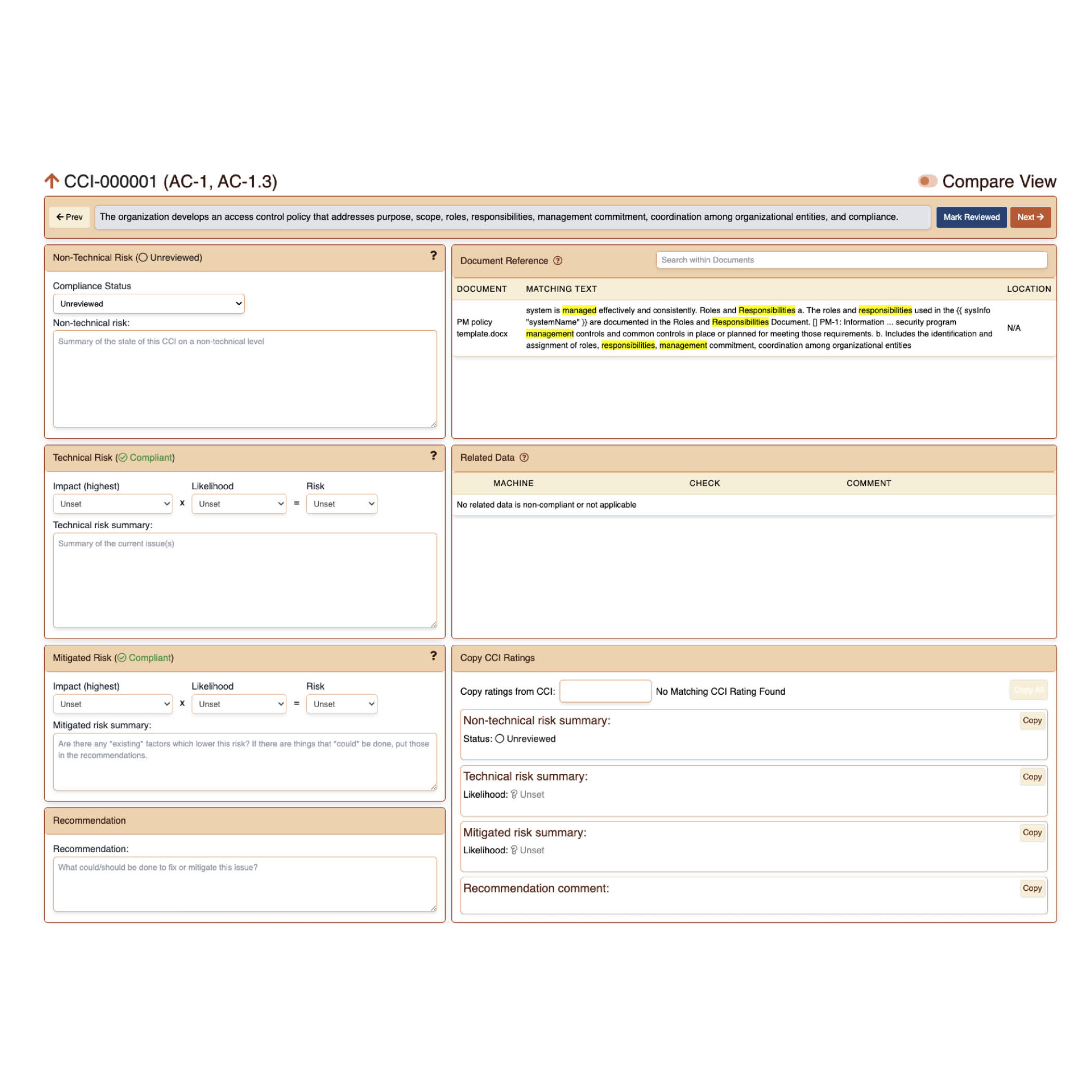
Supporting Technology: Xylok Security Suite
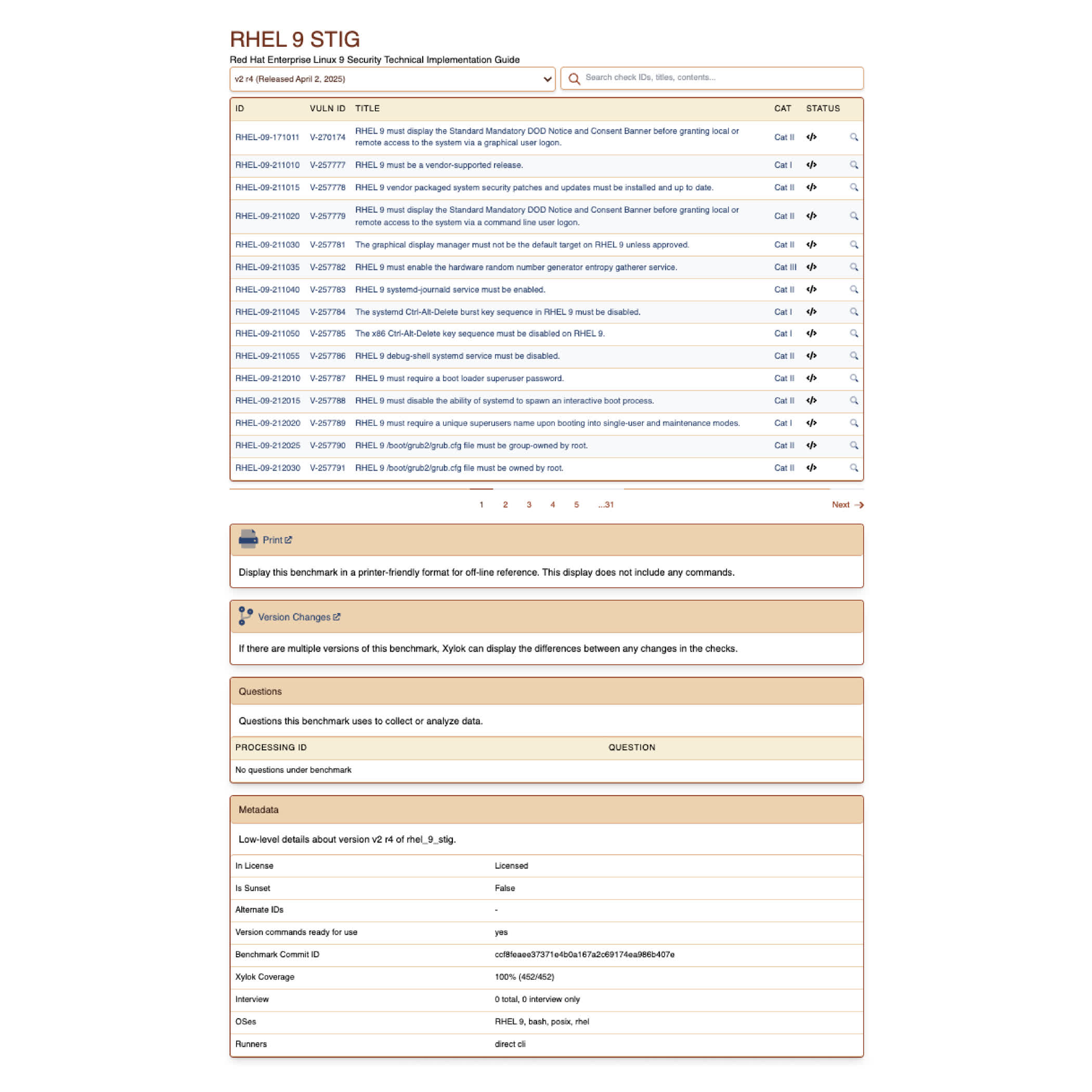
- Automated STIG and configuration validation
- Mapping to RMF and NIST controls
- Integrated evidence tracking and reporting
- Support for both technical and non-technical controls
CMMC Compliance Simplified
Start Your CMMC Readiness
Whether you are beginning your CMMC effort or preparing for a near-term assessment, Xylok provides a structured, defensible path to certification. Schedule a consultation to assess your readiness and define your path forward
Defense Cybersecurity Certification
CMMC Compliance Preparation and Assessment
The Cybersecurity Maturity Model Certification (CMMC) framework establishes cybersecurity standards for organizations in the Defense Industrial Base, creating specific certification requirements validated through third-party assessments.

CMMC Readiness Assessment
Systematic preparation for CMMC certification that addresses all applicable requirements.
- CMMC Level Assessment against requirements
- Gap Analysis and Remediation with prioritized plans

DOD Contractor Compliance Requirements
Specialized expertise in DOD contractor compliance requirements.
- Supply Chain Security Requirements
- Third-Party Assessment Preparation
Simplifying government and defense cybersecurity compliance
Transform Your Data Strategy
Convert your data obstacles into business advantages through customized solutions that address your industry-specific requirements.
See the Xylok Security Suite in action.
Get detailed pricing with our transparent model.
Explore STIGs and Controls.